Threat Actors Advertised NtKiller Malware on Dark Web Claiming Terminate Antivirus and EDR Bypass

A newly advertised underground tool called NtKiller is drawing attention on cybercrime forums after being promoted by a threat actor known as AlphaGhoul.
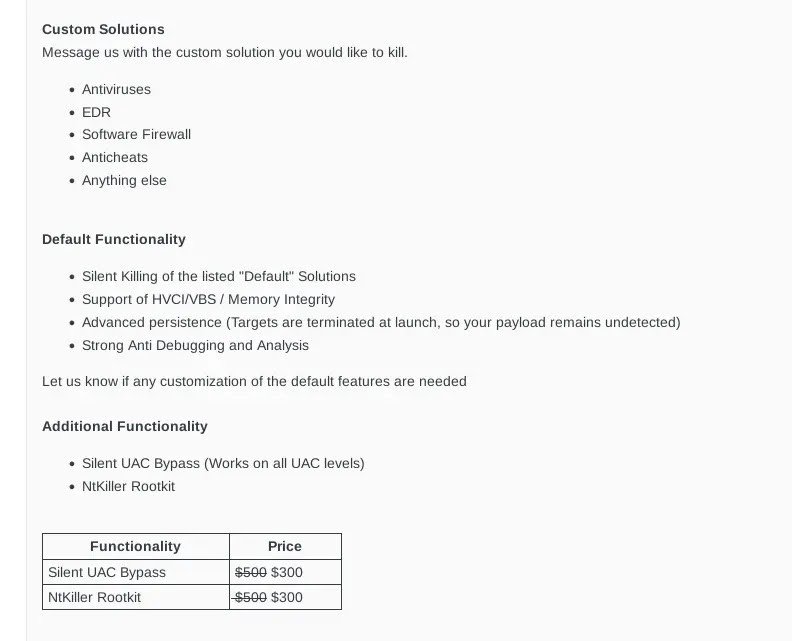
NtKiller is described as a tool that can silently shut down antivirus and EDR protections, making it attractive to attackers who want to operate without being detected. It is marketed as a “defensive bypass enabler” and appears aimed at malware developers and offensive operators looking for stronger evasion techniques.
According to the seller, NtKiller can bypass advanced Windows security features such as VBS, HVCI, and Memory Integrity—protections that normally prevent malicious drivers or unauthorized code from running. If true, this would allow attackers to stay active even on heavily secured systems.
One of the most concerning claims is early-boot execution, which allows the malware to load before most security tools are fully active. This approach is commonly seen in rootkits and gives attackers long-term control over compromised machines. The tool is also said to include anti-analysis and anti-debugging features, making investigation and detection more difficult for security teams.
Additional features include a silent UAC bypass to gain administrative privileges without user interaction, and an optional rootkit module designed to hide malicious activity from monitoring tools. The seller claims compatibility with well-known security products such as Microsoft Defender, ESET, Kaspersky, Bitdefender, and Trend Micro.
NtKiller is priced at $500 for the core tool, with optional modules costing $300 each, bringing the full package to $1,100. This pricing and modular structure reflect the growing professionalism of today’s underground malware market.
While these claims have not yet been independently verified, security researchers warn that tools like NtKiller highlight a clear trend: attackers are increasingly focused on disabling defenses first, rather than just exploiting vulnerabilities.
⚠️ Unverified but Potentially Dangerous
While the claims made by AlphaGhoul are concerning, they have not yet been independently verified by security researchers. It is common for underground sellers to exaggerate capabilities to attract buyers.
That said, the level of detail—especially references to bypassing VBS and Memory Integrity—makes this tool worth close attention. If NtKiller functions as advertised, it could pose a serious risk to organizations that rely solely on endpoint agents for protection.
Security teams should remain alert for signs of defense tampering, such as unexpected security service terminations or the installation of vulnerable or unsigned drivers, which are often early indicators of such attacks.
🔐 This reinforces the importance of layered security, strong privilege controls, and monitoring for security tool tampering.
Hackbit Hackers Academy Microsoft Security Fortinet
#Malware #EDR #EndpointSecurity #DefenseEvasion